- cka-exam'이라는 namespace를 만들고, 'cka-exam' namespace에 아래와 같은 Pod를 생성하시오. • pod Name: pod-01 • image: busybox • 환경변수 : CERT = "CKA-cert" • command: /bin/sh • args: -c "while true; do echo $(CERT); sleep 10;done"
// 네임스페이스 변경
$ kubectl config set-context --current --namespace=네임스페이스
// 네임스페이스 조회
$ kubectl config get-contexts
https://stackoverflow.com/questions/55373686/how-to-switch-namespace-in-kubernetes
static pod
API 서버 없이 특정 노드에 있는 kubelet 에 의해 직접 관리 /etc/kubernetes/manifests/ 디렉토리에 pod yaml 파일을 저장 시 적용됨
static pod 디렉토리 구성
# cat /var/lib/kubelet/config.yaml
…
staticPodPath: /etc/kubernetes/manifests
/etc/kubernetes/manifests에 yaml 추가 시 pod 생성, yaml 파일 삭제 시 Pod 삭제 (자동으로)
multi-container
sidecar-container
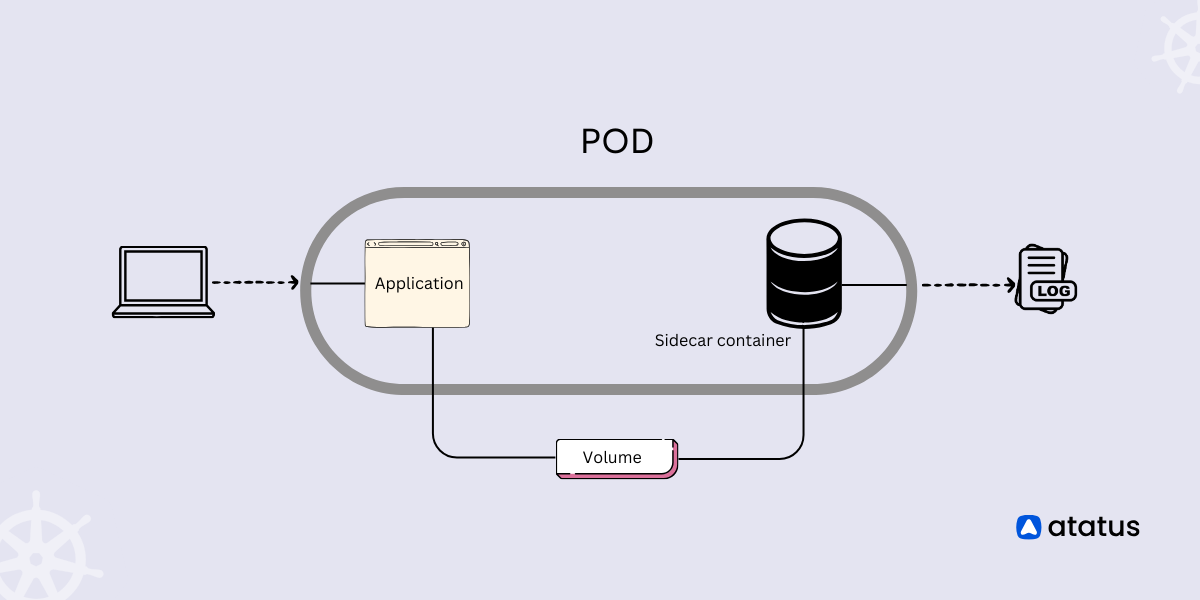
기본 컨테이너 기능을 확장하기 위해 사용 본래의 컨테이너는 기본 서비스에 충실하고, 추가 기능을 별도의 컨테이너를 이용해 적용
apiVersion: apps/v1
kind: Deployment
metadata:
name: myapp
labels:
app: myapp
spec:
replicas: 1
selector:
matchLabels:
app: myapp
template:
metadata:
labels:
app: myapp
spec:
containers:
- name: myapp
image: alpine:latest
command:
[
"sh",
"-c",
'while true; do echo "logging" >> /opt/logs.txt; sleep 1; done',
]
volumeMounts:
- name: data
mountPath: /opt
initContainers:
- name: logshipper
image: alpine:latest
restartPolicy: Always
command: ["sh", "-c", "tail -F /opt/logs.txt"]
volumeMounts:
- name: data
mountPath: /opt
volumes:
- name: data
emptyDir: {}
https://kubernetes.io/docs/concepts/workloads/pods/sidecar-containers/